The cloud platform that powers millions of web apps just had a very bad Saturday. Here’s everything that went down.

Wait, What Even Is Vercel?
If you’ve ever used a slick, fast-loading web app — there’s a decent chance Vercel had something to do with it. Vercel is a cloud development platform that hosts and deploys web applications. It’s the company behind Next.js, one of the most popular React frameworks on the planet. Developers love it for its serverless functions, edge computing, and CI/CD pipelines that make shipping code feel almost effortless.
In short? Vercel is infrastructure. It’s the invisible backbone behind a lot of the modern web. So when something goes wrong at Vercel, it doesn’t just affect one company. It ripples outward — fast.
And on April 19, 2026, something went very wrong.
The Breach Drops — On a Saturday
Nobody wants to deal with a security incident on a weekend. Vercel didn’t get that luxury.
On April 19, the company published a security bulletin confirming what many in the tech community were already buzzing about: unauthorized access to certain internal Vercel systems. The statement was short, measured, and a little alarming.
“We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems,” the company wrote. “We are actively investigating, and we have engaged incident response experts to help investigate and remediate. We have notified law enforcement.”
Law enforcement. That’s not a phrase companies throw around lightly.
Vercel was quick to add that its core services remained operational. But the damage? That was still being tallied. And the story was just getting started.
ShinyHunters Shows Up — Again
Before Vercel even published its bulletin, a threat actor had already beaten them to the punch. Someone claiming to be a member of ShinyHunters — the same black-hat hacking group linked to the Rockstar Games breach — posted on a hacking forum claiming they had breached Vercel and were ready to sell the goods.
The price tag? A cool $2 million.
According to BleepingComputer, the forum post claimed the attacker had access to:
- Multiple employee accounts with access to internal deployments
- API keys, including NPM tokens and GitHub tokens
- Source code and database data
- Access to internal deployments
As proof, the attacker shared a text file containing 580 data records of Vercel employee information — names, email addresses, account statuses, and activity timestamps. They also dropped a screenshot of what appeared to be an internal Vercel Enterprise dashboard.
Dark Web Informer, a threat intelligence account on X, flagged the activity early, pointing the finger squarely at ShinyHunters. One AI and tech expert put it bluntly: “They’re selling internal DB + employee accounts + GitHub/NPM tokens for $2M on BreachForums.”
It’s worth noting: threat actors linked to recent ShinyHunters attacks told BleepingComputer they were not involved in this specific incident. Whether that’s true or just distancing tactics — nobody knows for sure yet.
The Culprit? A Third-Party AI Tool
Here’s where things get genuinely wild. And a little ironic.
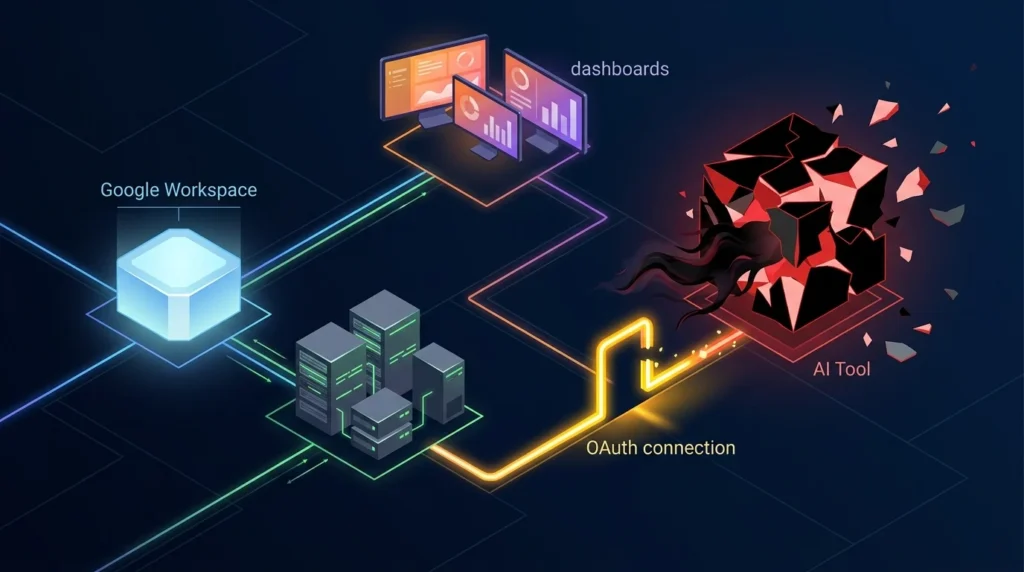
Vercel’s investigation revealed that the breach didn’t start with a brute-force attack or some sophisticated zero-day exploit. It started with a compromised third-party AI tool.
Specifically, a Google Workspace OAuth application belonging to an AI platform called Context.ai was compromised. That app had been granted access to a Vercel employee’s Google Workspace account. Once the attackers got into Context.ai’s OAuth app, they used it as a stepping stone — pivoting from the employee’s Google account directly into Vercel’s internal environments.
Vercel CEO Guillermo Rauch confirmed this on X, explaining that the attacker escalated access from the compromised account into Vercel environments, where they found environment variables that weren’t marked as “sensitive” — and therefore weren’t encrypted at rest.
Vercel even published a specific OAuth app identifier for Google Workspace admins to check:
OAuth App: 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
If you’re a Google Workspace admin, go check that right now. Seriously.
The “Non-Sensitive” Variable Problem
Let’s talk about the technical detail that made this breach worse than it needed to be.
Vercel stores all customer environment variables fully encrypted at rest. That’s good. But the platform also allows users to designate certain variables as “non-sensitive” — meaning they’re not encrypted with the same level of protection. The idea is that non-sensitive variables contain things like feature flags or public configuration values. Nothing critical.
Except that’s not always how it plays out in practice.
“We do have a capability to designate environment variables as ‘non-sensitive,'” Rauch explained. “Unfortunately, the attacker got further access through their enumeration.”
In plain English: the attacker poked around in the non-sensitive variables and found things they shouldn’t have. API keys. Tokens. Credentials that developers had stored there without flagging them as sensitive.
It’s a painful reminder that security is only as strong as its weakest configuration. One checkbox — or the absence of one — can unravel a lot of protection.
What Got Hit — And What Didn’t
Let’s be clear about the scope here, because it matters.
According to The Verge, the breach impacted a “limited subset” of Vercel’s customers. Developer Theo Browne noted that Vercel’s Linear and GitHub integrations bore the brunt of the attack. Environment variables marked as “sensitive” within the platform remained protected.
Vercel also confirmed that Next.js, Turbopack, and its other open-source projects are safe. No tampering with the codebase. No supply chain compromise — at least none that’s been detected so far.
The company’s services stayed up throughout the incident. No widespread outages. No cascading failures. That’s actually a testament to Vercel’s infrastructure resilience, even if the security side took a hit.
Why Crypto and Web3 Projects Should Be Paying Attention
Here’s a dimension of this story that’s flying under the radar for a lot of people.
Vercel is enormously popular in the crypto and Web3 space. Wallet connectors, decentralized application frontends, DeFi dashboards — a huge chunk of them run on Vercel. As BeInCrypto reported, projects storing API keys, private RPC endpoints, or wallet-related secrets in non-sensitive environment variables face real exposure risk.
Now, to be clear: the breach doesn’t threaten blockchains or smart contracts directly. Those operate independently of frontend hosting. But compromised deployment pipelines could theoretically allow build tampering for affected accounts — meaning an attacker could potentially inject malicious code into a Web3 frontend before it gets deployed to users.
No evidence of that has surfaced yet. But the possibility is enough to make any Web3 developer sweat.
The incident is a sharp reminder of a fundamental tension in the crypto world: you can build a perfectly decentralized protocol, but if your frontend runs on centralized infrastructure, you’ve still got a centralized attack surface.
What Vercel Is Doing About It
To their credit, Vercel moved quickly once the breach was confirmed.
The company engaged incident response experts, notified law enforcement, and published a detailed security bulletin. They also rolled out immediate updates to their dashboard, including:
- A new overview page for environment variables
- An improved interface for managing sensitive environment variables
Vercel is urging all customers — not just affected ones — to take the following steps:
- Review your environment variables for any sensitive information that isn’t flagged as sensitive
- Enable the sensitive variable feature to ensure proper encryption at rest
- Rotate any secrets that may have been exposed — API keys, tokens, credentials
- Regenerate GitHub tokens tied to Vercel integrations
- Audit recent build logs for cached credentials
Google Workspace admins should also check immediately for usage of the compromised OAuth app listed above.
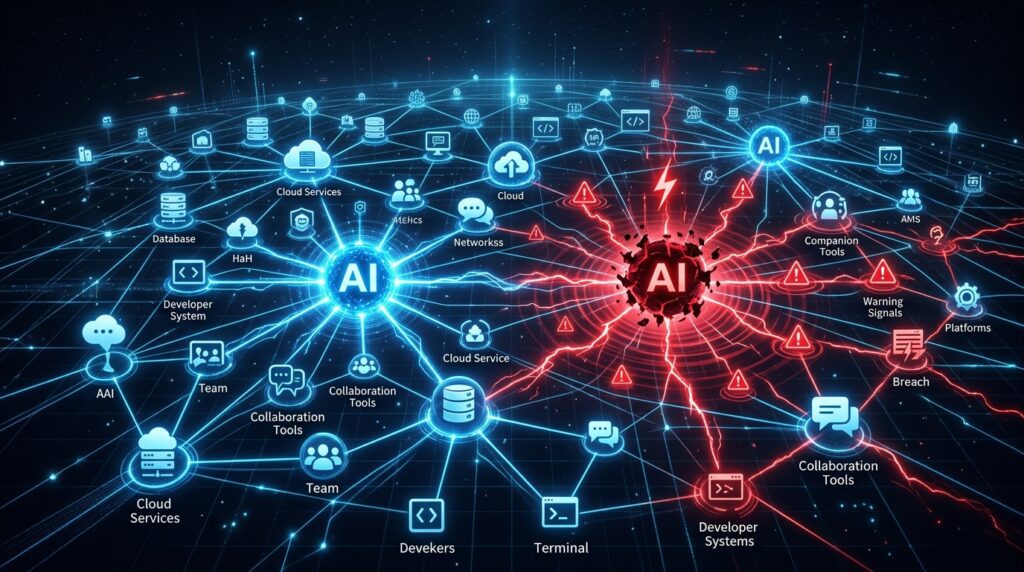
The Bigger Picture: AI Tools Are Now an Attack Vector
Step back for a second and look at what just happened here.
A major cloud platform got breached — not through a direct attack on its own systems, but through a third-party AI tool that had OAuth access to an employee’s Google account. The AI tool was the weak link. The AI tool was the door.
This is a new and genuinely concerning attack pattern. As companies integrate more and more AI tools into their workflows — and those tools request OAuth access to Google Workspace, GitHub, Slack, and other critical systems — each one of those integrations becomes a potential entry point for attackers.
Vercel’s investigation noted that the breach from Context.ai’s compromised OAuth app “potentially affected hundreds of its users across many organizations.” This wasn’t just a Vercel problem. It was a supply chain problem wearing an AI costume.
The lesson here isn’t “don’t use AI tools.” The lesson is: audit your OAuth integrations regularly. Know what apps have access to your Google Workspace. Revoke anything you don’t actively use. And for the love of all things secure, mark your sensitive environment variables as sensitive.
Final Thoughts
The Vercel breach is a fascinating and frustrating case study in modern security. The attacker didn’t need to be a genius. They didn’t need to crack encryption or exploit a zero-day. They just needed one compromised AI tool, one OAuth connection, and one employee’s Google account.
From there, they walked right in.
The good news: Vercel’s core infrastructure held. Open-source projects are safe. Services stayed online. And the company responded with transparency and speed.
The bad news: 580 employee records are floating around on hacking forums. Someone is asking $2 million for stolen data. And the full scope of affected customers is still being determined.
Stay tuned. This story isn’t over yet.