A wildly popular AI agent tool just handed attackers the keys to the kingdom — and 63% of users left the front door wide open.
Meet OpenClaw: The AI Agent That Does Everything
Let’s start with the basics. OpenClaw is one of the hottest AI agentic tools in the developer community right now. It’s the kind of tool that makes you feel like you’re living in a sci-fi movie. You give it access to your files, your apps, your accounts — and it acts on your behalf. Automatically. Intelligently. Powerfully.
Sounds amazing, right?
It is. That’s exactly why so many developers, hobbyists, and enterprises have been rushing to set it up. Over on the Level1Techs forum, users are actively sharing their OpenClaw setups — configuring Ollama, setting up email interactions, running it on dedicated Linux machines. One user even got their OpenClaw instance to reply with “Can’t do that, Dave” when it doesn’t know an answer. Charming. Nerdy. Absolutely delightful.
But here’s the thing. OpenClaw creator Peter Steinberger warned users from day one on GitHub: “There is no ‘perfectly secure’ setup.” That wasn’t just a disclaimer. That was a prophecy.
And now, that prophecy has come true — in spectacular, terrifying fashion.
CVE-2026-33579: The Flaw That Scored a 9.8 Out of 10
Buckle up, because this one is a doozy.
Researchers at AI app-builder Blink discovered a privilege escalation vulnerability in OpenClaw’s device pairing system. They named it CVE-2026-33579. It scored a jaw-dropping 9.8 out of 10 on the CVSS severity scale. Some sources even peg it at 9.9 — Critical.
What does that mean in plain English? It means this vulnerability is about as bad as it gets.
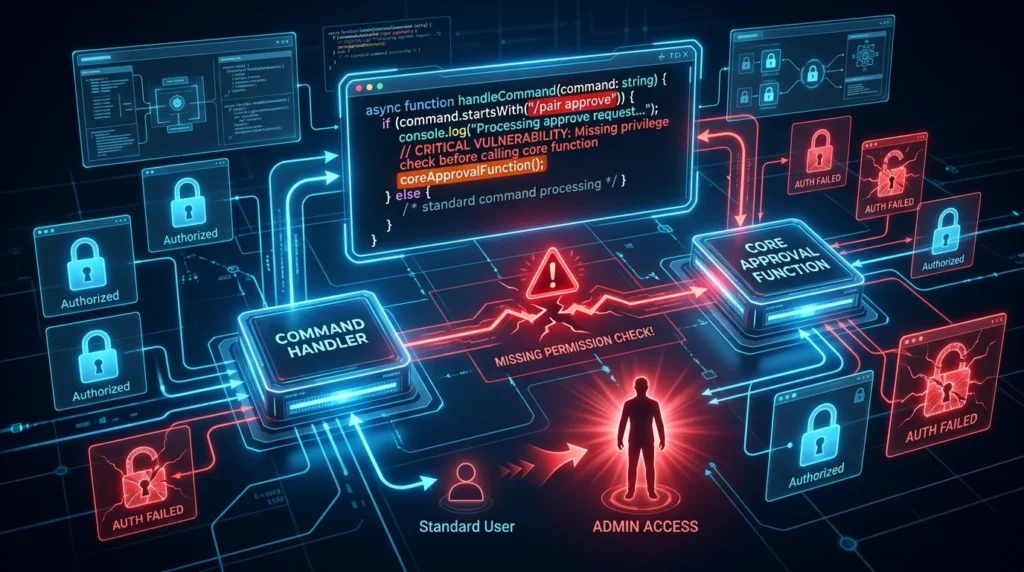
Here’s the scary part. The flaw lives in OpenClaw’s /pair approve command path. When a user requests device pairing, the system checks the request — but it never checks who is doing the approving. The approval function, as Blink put it bluntly, “has no information about who is approving. It only sees the device pairing request itself.”
So what happens? An attacker with the absolute lowest level of access — just basic pairing privileges — can simply ask for full admin access and then approve their own request. No hacking wizardry required No special tools. No user interaction needed. Just ask, approve, done.
The door was unlocked from the inside the whole time.
The Numbers Are Genuinely Alarming

Here’s where things go from bad to worse.
Blink researchers scanned the internet and found roughly 135,000 exposed OpenClaw instances. Of those, a staggering 63% were running with zero authentication. None. Zip. Nada.
That means an attacker didn’t even need a low-level account to start the exploit chain. They could walk in off the street — metaphorically speaking — and work their way up to full administrator. No credentials required. Just a network connection and bad intentions.
Mashable called it “frightening.” That’s not hyperbole. That’s accurate.
And what can a compromised admin account actually do? According to Blink’s analysis: read all connected data sources, steal credentials stored in the agent’s skill environment, execute arbitrary tool calls, and pivot to other connected services. The phrase “privilege escalation” genuinely undersells it. This is full instance takeover.
The Two-Day Gap That Made Everything Worse
Here’s a detail that should make every security professional’s blood run cold.
OpenClaw patched the vulnerability on March 29, 2026 with version 2026.3.28. But the official CVE listing didn’t appear on the National Vulnerability Database until March 31 — a full two days later.
Two days. That’s a two-day window where attackers who were watching the OpenClaw GitHub repository could have spotted the fix in the commit log, reverse-engineered the vulnerability, and started exploiting it — all before most users even knew there was a problem to fix.
Ars Technica’s Dan Goodin didn’t mince words. He told users to “assume compromise.” Not “maybe check your logs.” Not “consider updating.” Assume. Compromise.
That’s the cybersecurity equivalent of a fire alarm going off and someone saying, “You should probably assume the building is on fire.”
This Isn’t a One-Off Bug. It’s a Pattern.
Now here’s the part that should really make you sit up straight.
CVE-2026-33579 isn’t an isolated incident. According to The New Claw Times, this is the sixth pairing-related vulnerability disclosed in OpenClaw in just six weeks. Six. In six weeks.
All six vulnerabilities share the same root cause — a fundamental design flaw in how OpenClaw handles permissions. Each patch has fixed a specific exploit in isolation. But nobody has gone back and rearchitected the authorization system that keeps producing these flaws.
It’s like patching a leaky roof one drip at a time while ignoring the fact that the entire structure is compromised. You fix one hole, and three more appear.
There’s also a companion vulnerability — CVE-2026-32922, which scored an even more terrifying 9.9 Critical — that was fixed in version 2026.3.11. And before that, The New Claw Times reported on nine CVEs disclosed in just four days during early 2026, including a remote code execution flaw (CVE-2026-25253) that scored 8.8.
This isn’t a bug. It’s a pattern. And patterns don’t go away with a single patch.
How the Exploit Actually Works (The Technical Bit)
For the technically curious, here’s what’s actually happening under the hood.
The bug lives in two specific files in the OpenClaw codebase: the command handler for /pair approve in extensions/device-pair/index.ts and the core approval function in src/infra/device-pairing.ts. When a pairing approval gets triggered, the command handler retrieves the request and calls the core function — but it never passes the caller’s security scopes into that function.
Because operator.admin is a valid scope, any well-formed request for admin access passes validation and gets approved. The intended model — where an approver can only grant permissions they themselves hold — never actually executes.
The fix, found in commit e403decb6e, adds callerScopes to the approval function signature and enforces that requested device scopes must be a strict subset of the caller’s own scopes. Simple in theory. Catastrophic in practice when missing.
Discovery credit goes to AntAISecurityLab, per the NVD listing.
Real Users, Real Risks
Back on the Level1Techs forum, user SunDancer shared a refreshingly honest update about their OpenClaw setup. They installed it on a dedicated Linux machine, configured it with Ollama, and set up an email account to interact with it. They even asked their OpenClaw instance about CVE-2026-33579 directly.
The response? “I’m sorry Dave, I’m afraid I don’t know the answer to your question.”
Ironic. The tool at the center of a major security crisis couldn’t even explain the crisis to its own user.
To SunDancer’s credit, they had already applied the updates and isolated the instance on a dedicated network with no external interfaces. Smart. That’s exactly the kind of defense-in-depth thinking that security professionals recommend.
But not everyone is that careful. Most users aren’t running isolated networks. Most users aren’t auditing their activity logs. And most users — 63% of them, apparently — weren’t even running authentication in the first place.
What You Need to Do Right Now
Let’s cut straight to the action items. No fluff.
First: Update to OpenClaw version 2026.3.28 immediately. If you haven’t done this yet, stop reading and go do it now. We’ll wait.
Second: If you were running an older version at any point in the past week, treat your instance as potentially compromised. Don’t assume you’re fine. Assume you’re not.
Third: Audit your activity logs. Look specifically for suspicious /pair approval events. Any device approvals you don’t recognize are a red flag.
Fourth: Enable authentication if you haven’t already. The fact that 63% of instances were running without it is genuinely baffling. Turn it on.
Fifth: Ask yourself the hard question that both Mashable and Ars Technica are now raising — is the productivity gain from a tool this powerful worth the security surface it creates? That’s not a rhetorical question. It’s a real one that every team running OpenClaw in production needs to answer honestly.
The Bigger Picture: AI Agents and the Security Reckoning

Here’s the uncomfortable truth that this whole situation forces us to confront.
AI agentic tools are incredibly powerful. They’re also incredibly dangerous when they go wrong. OpenClaw isn’t unique in this regard — it’s just the most visible example right now. Any tool that gets full access to your files, accounts, and connected services is a massive attack surface. That’s the trade-off.
The developer community is learning this lesson in real time. The hard way.
Six vulnerabilities in six weeks isn’t just a bad look for OpenClaw. It’s a warning sign for the entire category of AI agent tools. The authorization models underpinning these systems need to be robust from the ground up — not patched reactively after each exploit surfaces.
As the Level1Techs community discussion shows, people are genuinely excited about what local AI agents can do. They’re setting up home labs, experimenting with document ingestion, building personal automation systems. That enthusiasm is wonderful. But enthusiasm without security awareness is a recipe for exactly the kind of disaster we’re seeing with CVE-2026-33579.
The future of AI agents is bright. But right now, the security foundations need serious work. Update your tools. Audit your systems. And maybe — just maybe — don’t leave 63% of your instances running without authentication.
Sources
- A Frightening OpenClaw Vulnerability Has Been Discovered — Mashable SEA
- CVE-2026-33579: OpenClaw Privilege Escalation Flaw Scores 9.8 — The New Claw Times
- CVE-2026-33579 Vulnerability Analysis & Exploit Details — Akaoma CVE Dashboard
- Where to Start with Local LLM/AI Models — Level1Techs Forum
- Here’s Why It’s Prudent for OpenClaw Users to Assume Compromise — Ars Technica
- CVE-2026-33579: OpenClaw Privilege Escalation Fix Guide — Blink
- GitHub Security Advisory GHSA-hc5h-pmr3-3497
Want your AI product explained to a large AI-native audience?
Kingy AI helps AI companies turn complex products into clear, useful YouTube videos that drive awareness, product understanding, demos, clicks, and search visibility.









Comments 1